UPDATE: this post restricts access based on source IP address. A new article shows how to restrict access (registrations) based on username.
Sutuation: you have to check the source address of REGISTER messages, going to your OpenSIPS server and decide wether to allow them or to deny.
Use permissions module for this.
You can use it in two variants:
1. with OpenSIPS’ text config files register.allow and register.deny (similar to Unix hosts.allow and hosts.deny).
In this case you should use module’s function ‘allow_register‘
Example of blocking REGISTERs from 10.145.13.49 IP address:
register.deny file:
ALL : "^sip:.*10\.145\.13\.49"
ALL : "^sip:.*0*10\.145\.0*13\.0*49" # this is to prevent bypassing
# by the insertion of one or more '0' in the IP address
register.allow file is empty (allow everything except those in .deny file).
OpenSIPS script snippet:
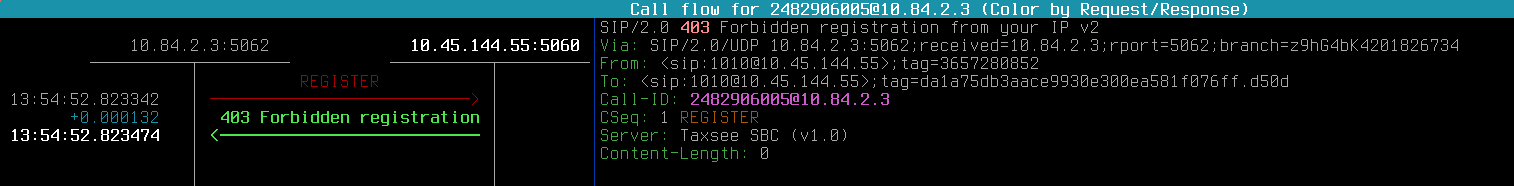
if ( is_method("REGISTER") ) {
if (allow_register("register")) {
save("location");
exit;
} else {
sl_send_reply("403", "Forbidden registration from your IP v2");
exit;
}
}
But this method has one big disadvantage – you need to restart OpenSIPS each time you edit register.allow/register.deny.
OpenSIPS ‘permissions’ module has a MI function ‘address_reload‘ but it reloads the table (see below), not the allow/deny files.
So, it’s more cool to use the second variant, go on reading!..
2. with DB table ‘address‘.
In this case you should use modules’ function ‘check_address‘
– register.allow and register.deny files are empty.
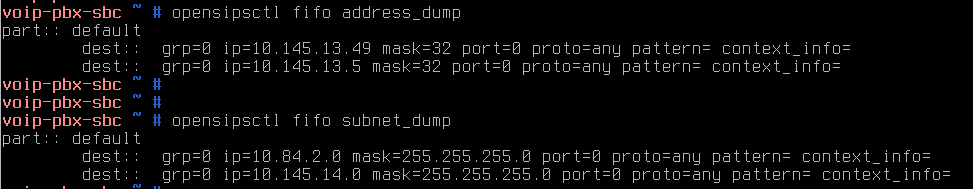
– add entries to ‘address’ table. In our case we’re using not real SQL DB but dbtext. So, this is how ‘/etc/opensips/dbtext/address’ file looks like:
voip-pbx-sbc ~ # cat /etc/opensips/dbtext/address
id(int,auto) grp(int) ip(string) mask(int) port(int) proto(string) pattern(string,null) context_info(string,null)
1:0:10.84.2.0:24:0:any
2:0:10.145.13.5:32:0:any
3:0:10.145.13.49:32:0:any
4:0:10.145.14.0:24:0:any
WARNING: every time you add any new table, do not forget to add it’s version to another table ‘version’:
voip-pbx-sbc ~ # cat /etc/opensips/dbtext/version
table_name(string) table_version(int)
dispatcher:8
load_balancer:2
address:5
Firstly, I haven’t done it, and that’s why OpenSIPS could not start and I had this message in the system log:
ERROR:core:db_check_table_version: invalid version 0 for table address found, expected 5
So, the script snippet with the ‘check_address’ function:
if ( is_method("REGISTER") ) {
if(check_address("0","$si","0","any")) {
save("location");
exit;
} else {
sl_send_reply("403", "Forbidden registration from your IP v2");
exit;
}
}
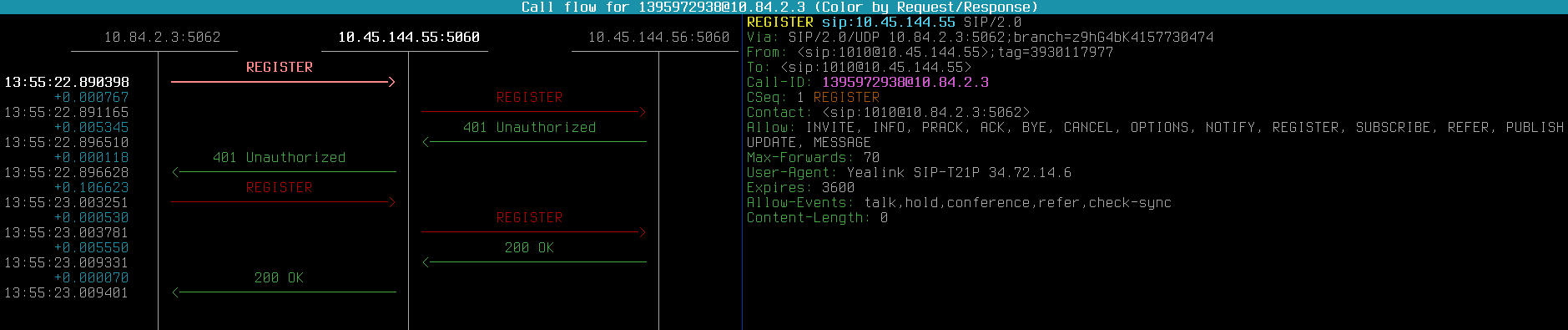
And here’s the magic! You may add IP-addresses or subnets to your DB or dbtext file and then run a MI command ‘address_reload‘ without restarting your high-loaded OpenSIPS.
Now the policy is “if address is in the table – allow it, otherwise block”. Look at the images below.
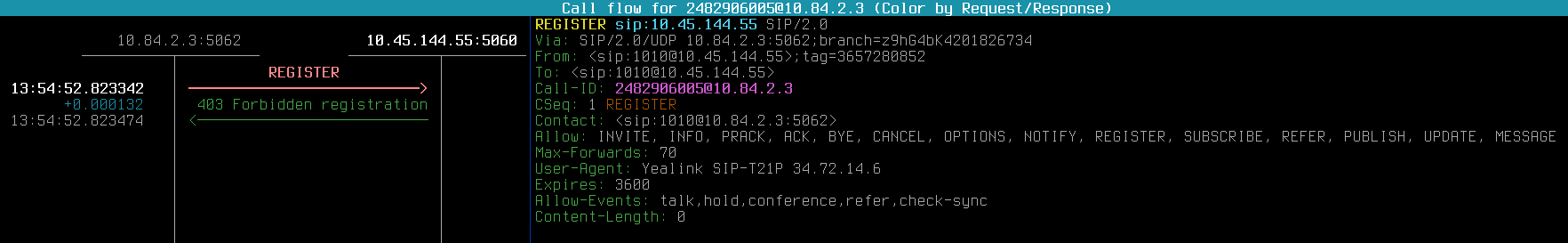
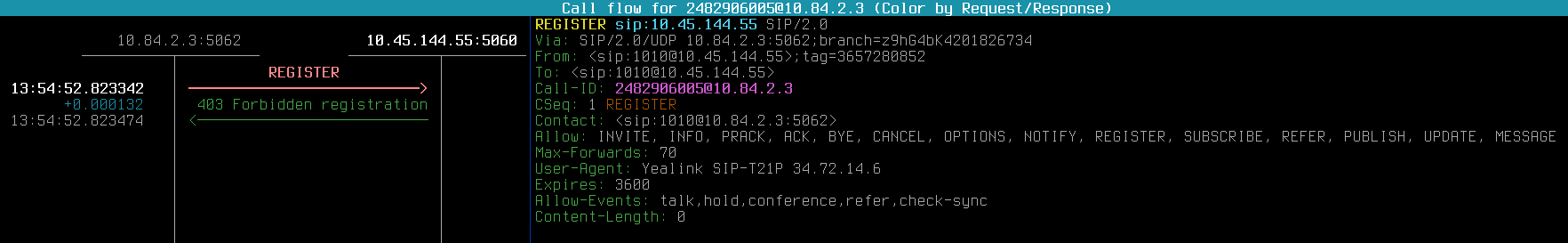
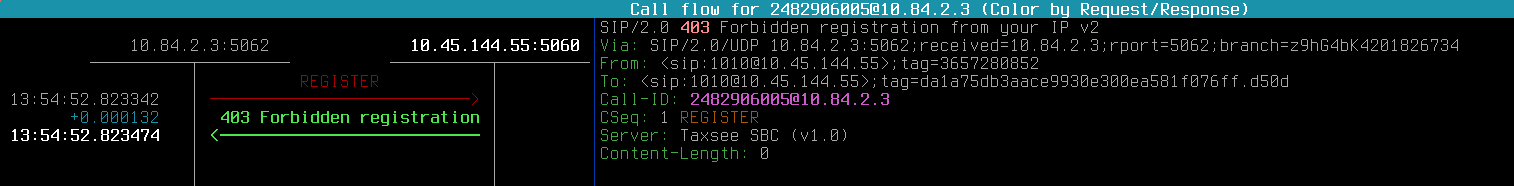
IP is not in the table – REGISTER is forbidden:
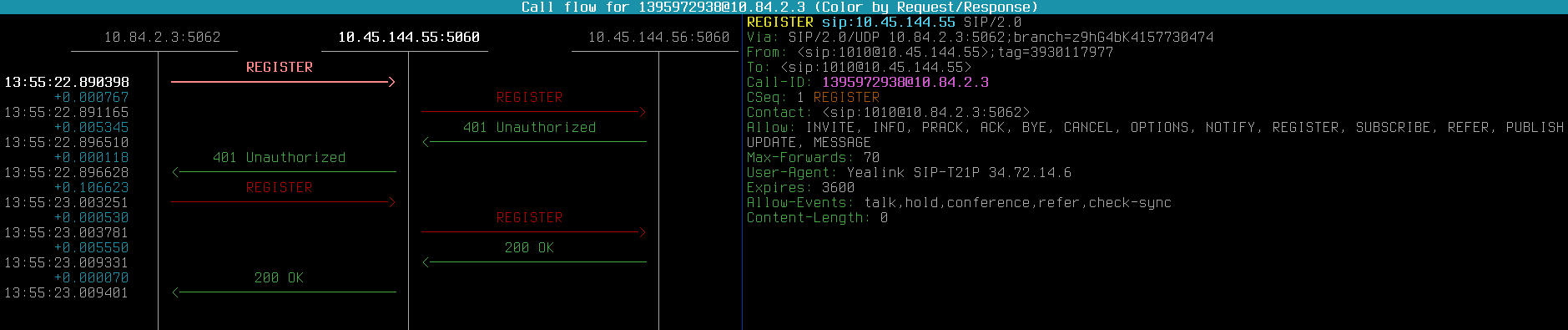
IP has been added to dbtext table and table reloaded – registrations passed successfully:
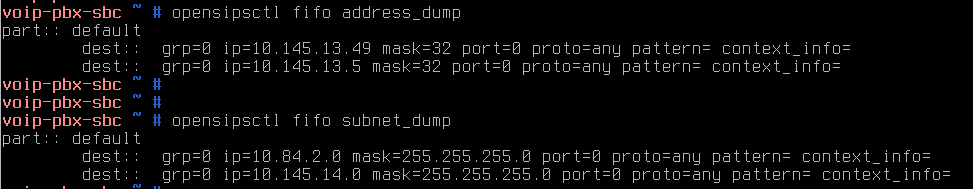
You can also look the table’s contents with MI commands ‘opensipsctl fifo address_dump‘ and ‘opensipsctl fifo subnet_dump‘.
UPD: OpenSIPS core developer’s answer to my question http://lists.opensips.org/pipermail/users/2017-October/038169.html .